In the previous four posts, I explained AWS Landing Zone in general, the structure of AWS organization, and basic security configurations:
Building a Landing zone with AWS Control Tower (part 1)
Building a Landing zone with AWS Control Tower (part 2)
Building a Landing zone with AWS Control Tower (part 3)
Control Tower Guardrails overview (Preventive, Detective, and Proactive)
Vanilla AWS Control Tower provides very basic things (but still very important) like AWS Config and AWS CloudTrail for the whole AWS organization and centralized logging into an isolated AWS account, but when it comes to more advanced automation and customization, we have several options:
- Customizations for AWS Control Tower (CfCT), which I already described in the article.
- Landing Zone Accelerator on AWS (LZA), which I will briefly show in this article, and compare it with the CfCT solution.
- AWS Control Tower Account Factory for Terraform (AFT) — Terraform-based automation.
Comparing Design
Customizations for AWS Control Tower (CfCT)
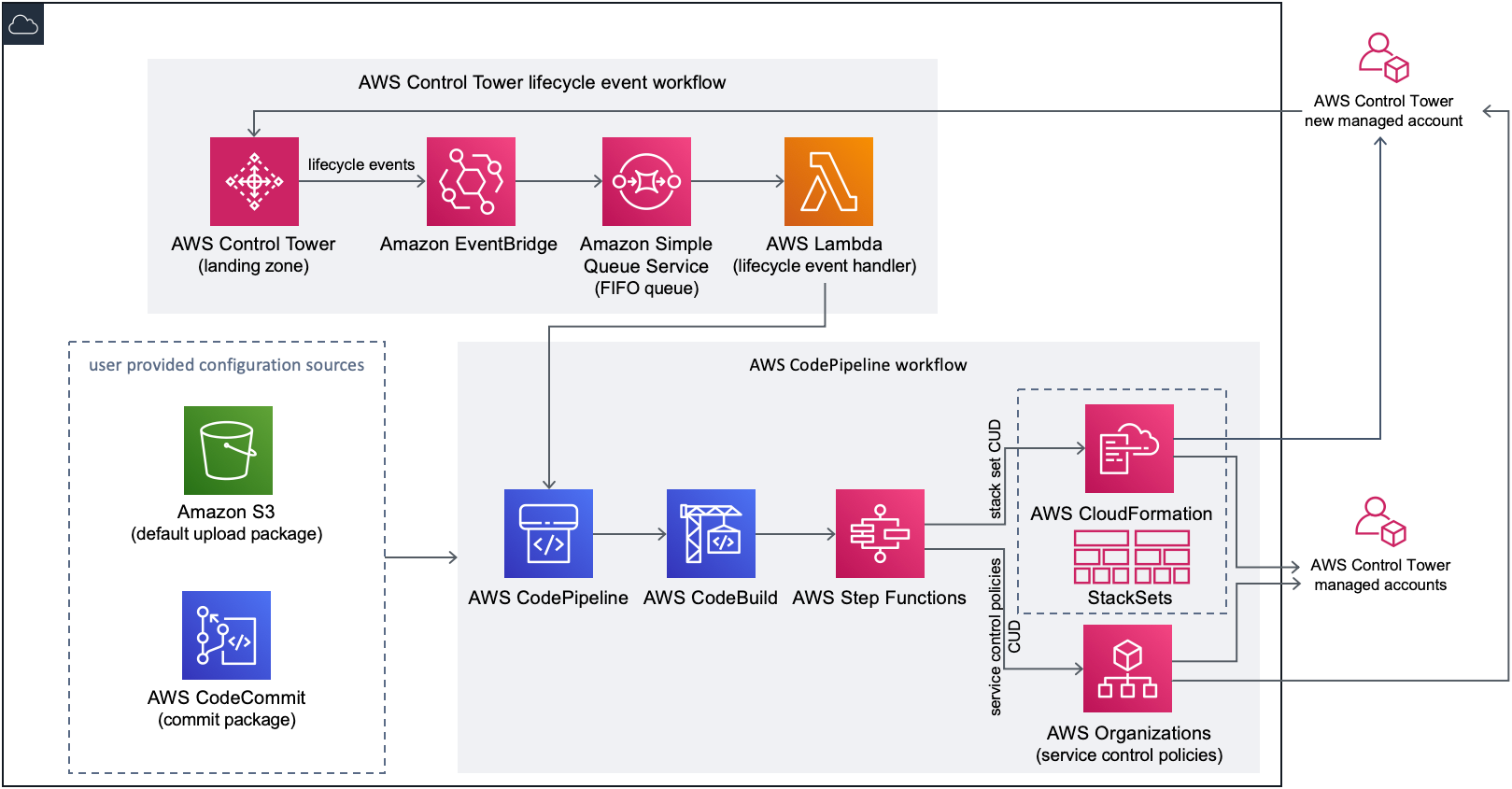
CfCT includes an AWS CloudFormation template that you deploy in your AWS Control Tower management account. The template launches all the necessary components to build the workflows, allowing you to customize your AWS Control Tower landing zone.
CfCT deploys two workflows:
- an AWS CodePipeline workflow
- and an AWS Control Tower lifecycle event workflow.
The AWS CodePipeline workflow
The AWS CodePipeline workflow configures AWS CodePipeline, AWS CodeBuild projects, and AWS Step Functions that orchestrate the management of AWS CloudFormation StackSets and SCPs in your organization.
When you upload the configuration package, CfCT invokes the code pipeline to run three stages.
- Build Stage — validates the contents of the configuration package using AWS CodeBuild.
- SCP Stage — invokes the service control policy state machine, which calls the AWS Organizations API to create SCPs.
- AWS CloudFormation Stage — invokes the stack set state machine to deploy the resources specified in the list of accounts or OUs, which you’ve provided in the manifest file.
At each stage, the code pipeline invokes the stack set and SCP step functions, which deploy custom stack sets and SCPs to the targeted individual accounts, or to an entire organizational unit.
The AWS Control Tower lifecycle event workflow
When a new account is created in AWS Control Tower, a lifecycle event can invoke the AWS CodePipeline workflow. You can customize the configuration package through this workflow, which consists of an Amazon EventBridge event rule, an Amazon Simple Queue Service (Amazon SQS) first-in first-out (FIFO) queue, and an AWS Lambda function.
When the Amazon EventBridge event rule detects a matching lifecycle event, it passes the event to the Amazon SQS FIFO queue, invokes the AWS Lambda function, and invokes the code pipeline to perform downstream deployment of stack sets and SCPs.
Landing Zone Accelerator on AWS
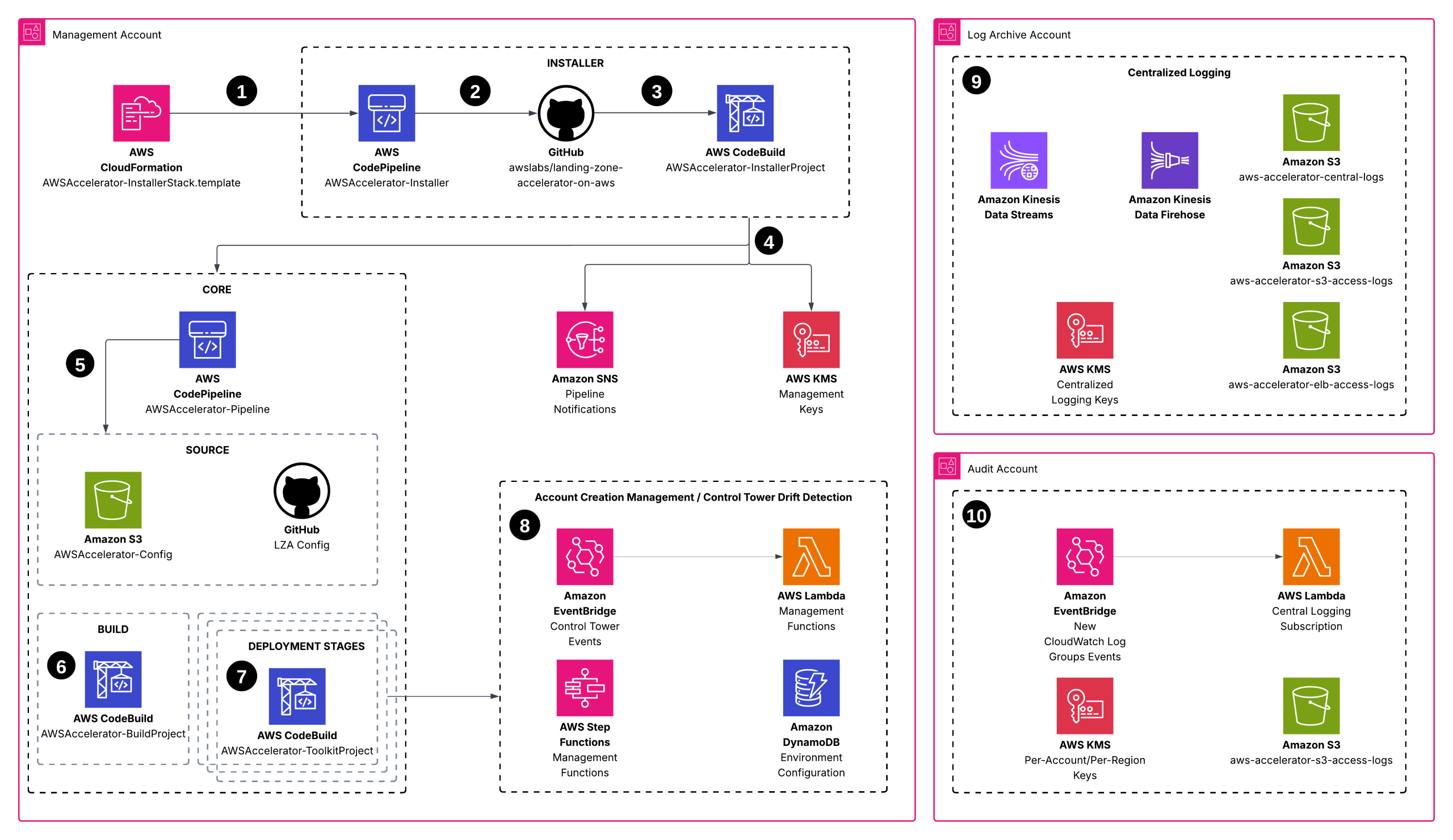
- You use AWS CloudFormation to install the solution into your environment. Your environment must meet prerequisites before deploying the solution. The provided CloudFormation template deploys an AWS CodePipeline that contains the Landing Zone Accelerator on the AWS installation engine.
- The Installer pipeline (AWSAccelerator-InstallerStack) operates independently of the Core pipeline. This way, you can update to future versions of the solution with a single parameter through the AWS CloudFormation console.
- An AWS CodeBuild project serves as an orchestration engine to build and run the solution’s AWS CDK application, which deploys the Core pipeline (AWSAccelerator-PipelineStack) and its associated dependencies.
- The solution deploys Amazon SNS topics that you can subscribe to for alerts on Core pipeline events, thereby increasing the observability of your Core pipeline operations. Additionally, the solution deploys two AWS KMS customer-managed keys to manage encryption at rest for the Installer and Core pipeline dependencies.
- The Core pipeline validates and synthesizes inputs and deploys additional CloudFormation stacks with AWS CDK. An Amazon Simple Storage Service (Amazon S3) bucket (aws-accelerator-config) stores the configuration files used by the solution. These configuration files are the primary mechanism for configuring and managing the solution.
- An AWS CodeBuild project compiles and validates the solution’s AWS CDK application configuration.
- Multiple AWS CodeBuild deployment stages deploy the resources that were defined in the solution configuration files to your multi-account environment. An optional manual review stage can be included, allowing you to view all the changes that will be applied by these stages.
- The solution deploys resources that monitor AWS Control Tower lifecycle events to detect potential drift against a known good state (in other words, when the actual configuration of an infrastructure resource differs from its expected configuration). The solution also deploys resources that can automate the enrollment of new AWS accounts into your multi-account environment. When using AWS Control Tower with this solution, ensure that accounts and organizational units (OUs) within your AWS Control Tower environment are properly enrolled. You can manage this through the AWS Control Tower console.
- The solution deploys centralized logging resources in the Log Archive account in your multi-account environment. This includes Amazon Kinesis resources for streaming and ingesting logs, AWS KMS keys to facilitate encryption at rest, and Amazon Simple Storage Service (Amazon S3) buckets as log storage destinations.
- The solution provisions the audit account with resources to Amazon CloudWatch log groups, sending them to the centralized logging infrastructure in the LogArchive account.
Comparison
CfCT looks much easier and lighter than LZA, and Pipeline itself is smaller:
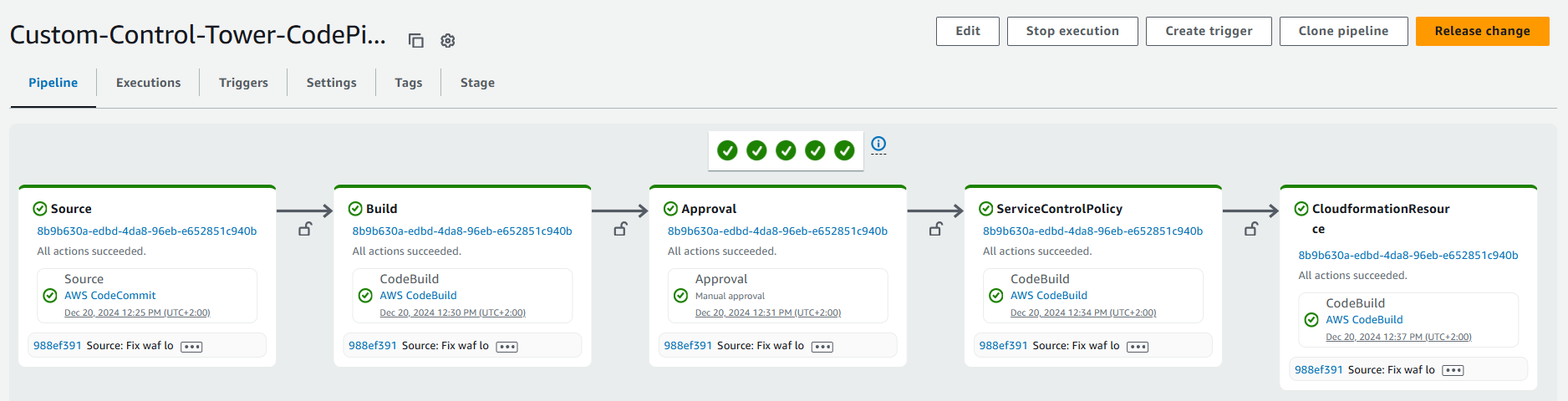
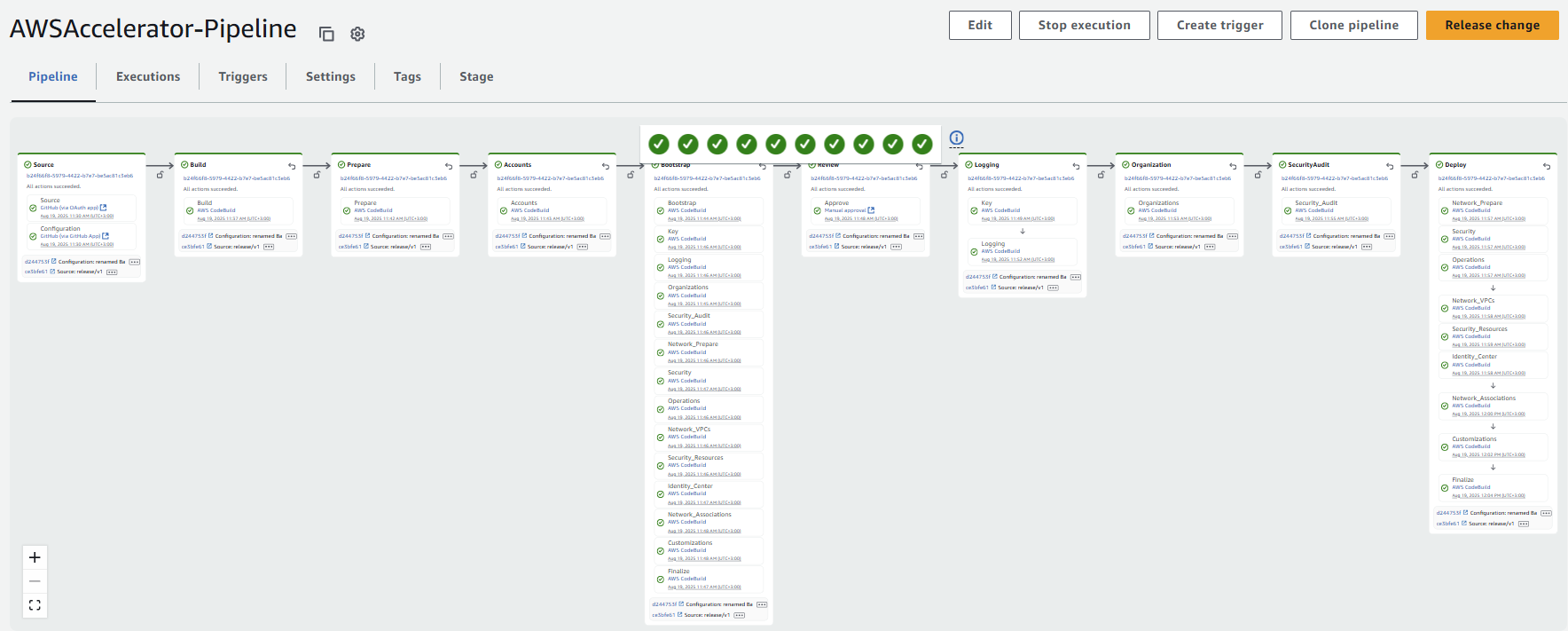
However, jumping ahead, LZA will take on much more responsibility later, when additional customization needs to be added to your Landing Zone.
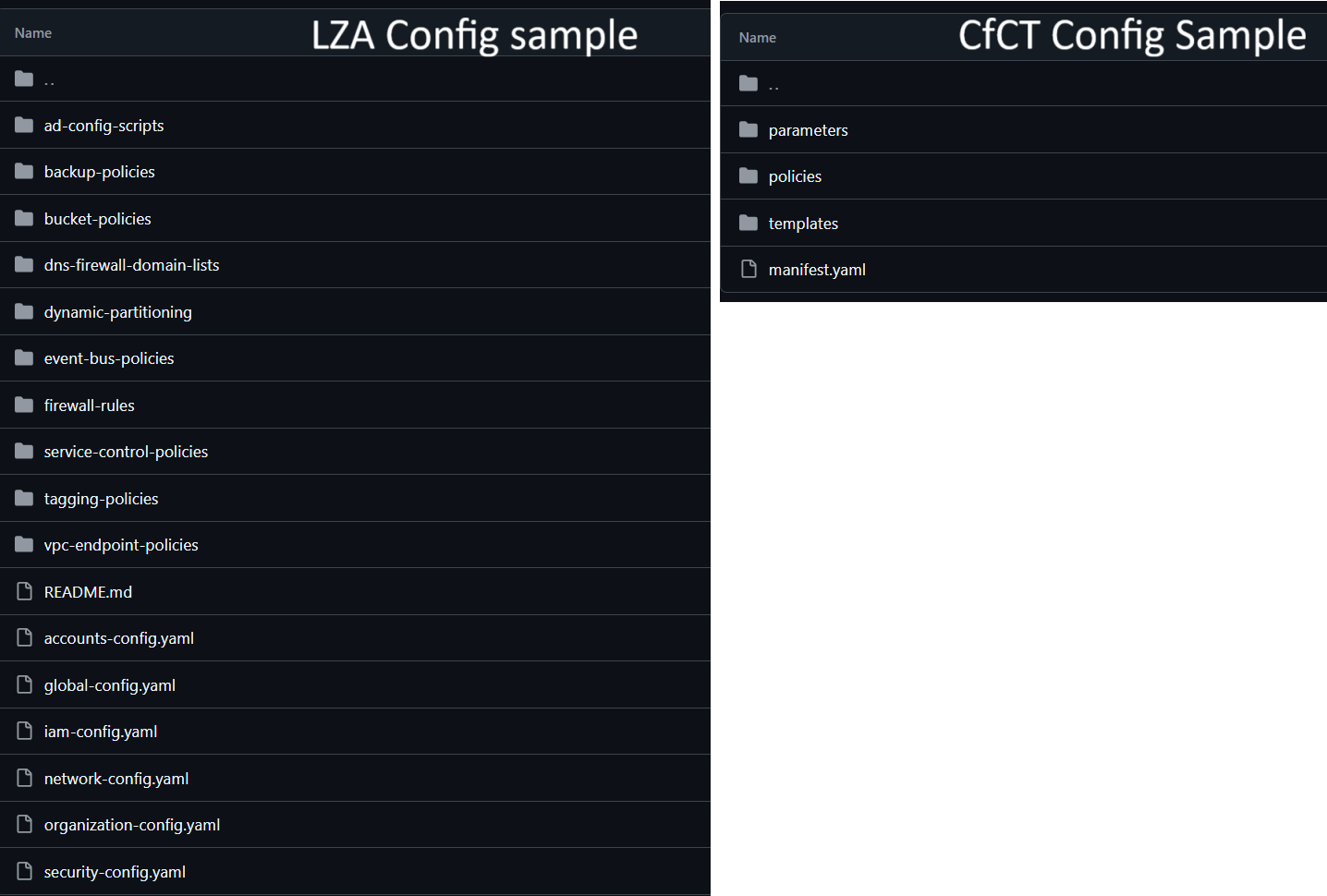
Comparing Configuration Files
Overall, LZA contains 6 mandatory config files (YAML):
- organization-config.yaml
- accounts-config.yaml
- global-config.yaml
- iam-config.yaml
- network-config.yaml
- security-config.yaml
While CfCT contains one:
- manifest.yaml + set of CloudFormation templates you need
Here is a comparison of sample configs, available on GitHub:
Comparing Capabilities
CfCT allows you to deploy CloudFormation templates via CloudFormation StackSets to the required AWS Accounts and Regions + Apply Service Control Policies (SCP) and Resource control policies (RCP) to the required Organizational Units and Accounts.
LZA gives you ALL of these + creating new AWS Accounts and Organizational units, enabling Guardrails (Controls) via configuration file, enabling AWS Security services without providing CloudFormation templates (some internal magic), deploying centralized networking, and many other essential things which we often see in the customer’s requirements for a Landing Zone.
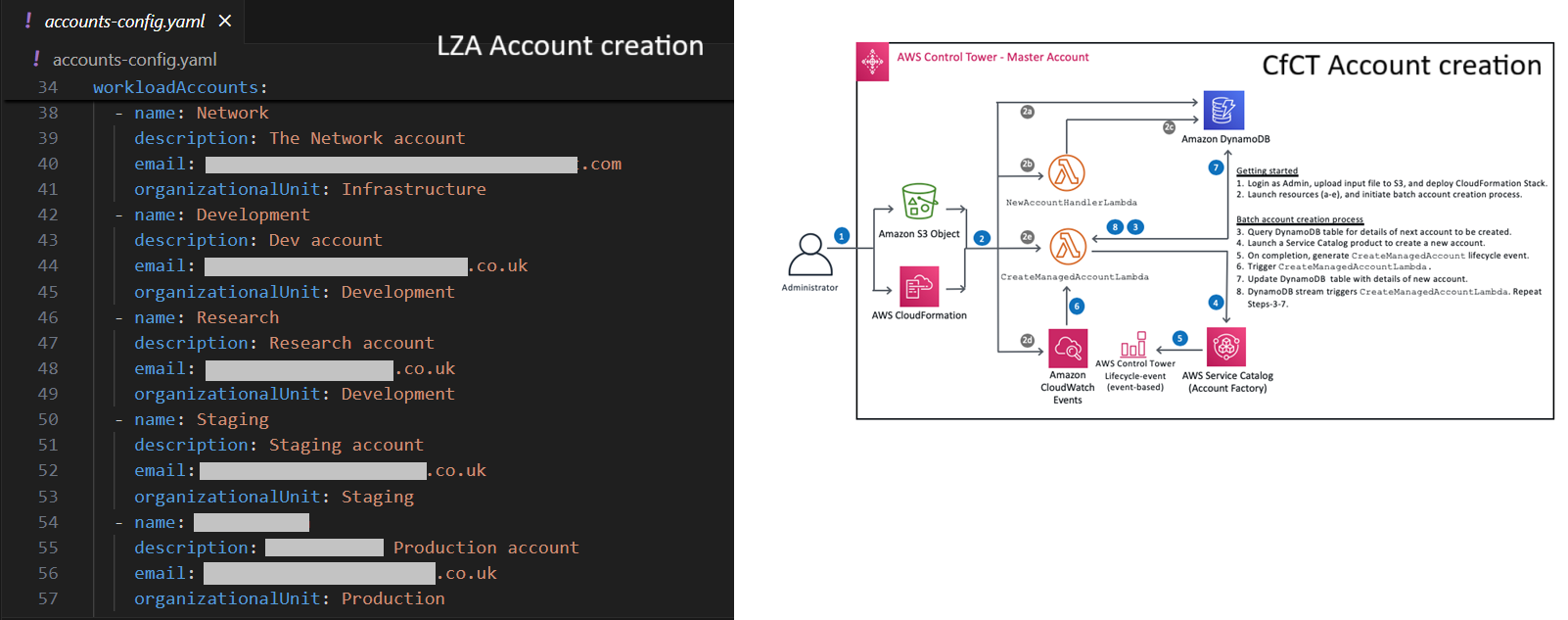
In LZA, you can add a new account with a couple of lines in a simple config file, while CfCT requires a separate solution or adding accounts manually:
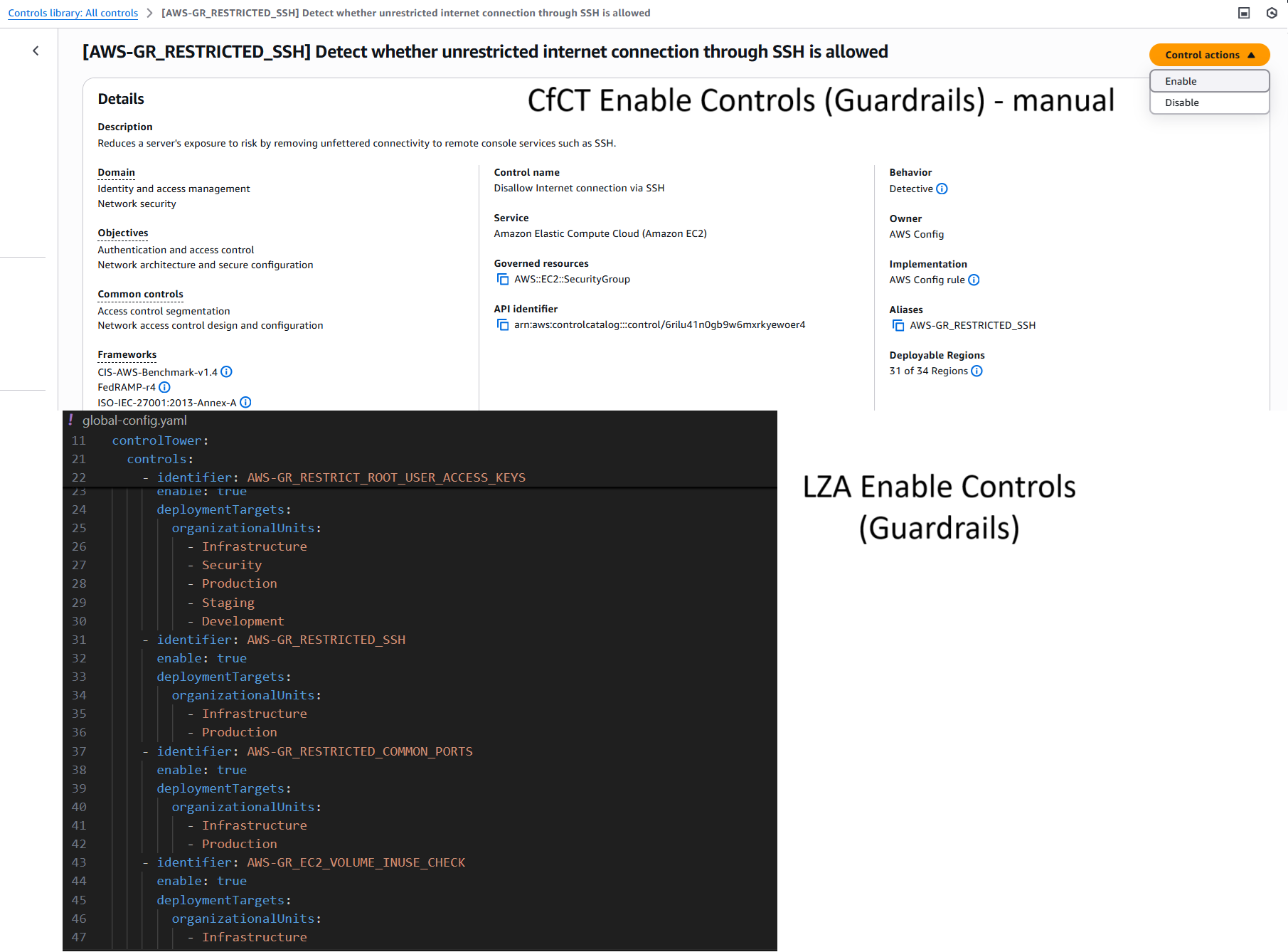
In LZA, you can enable Controls (Guardrails) with a couple of lines in a simple config file, while CfCT does not provide such a capability at all, so you will need to do it manually, or use separate automation:
In LZA, you can enable GuardDuty with a couple of lines in a simple config file, while in CfCT, you need a CloudFormation template defining the GuardDuty + add a section in the manifest file:
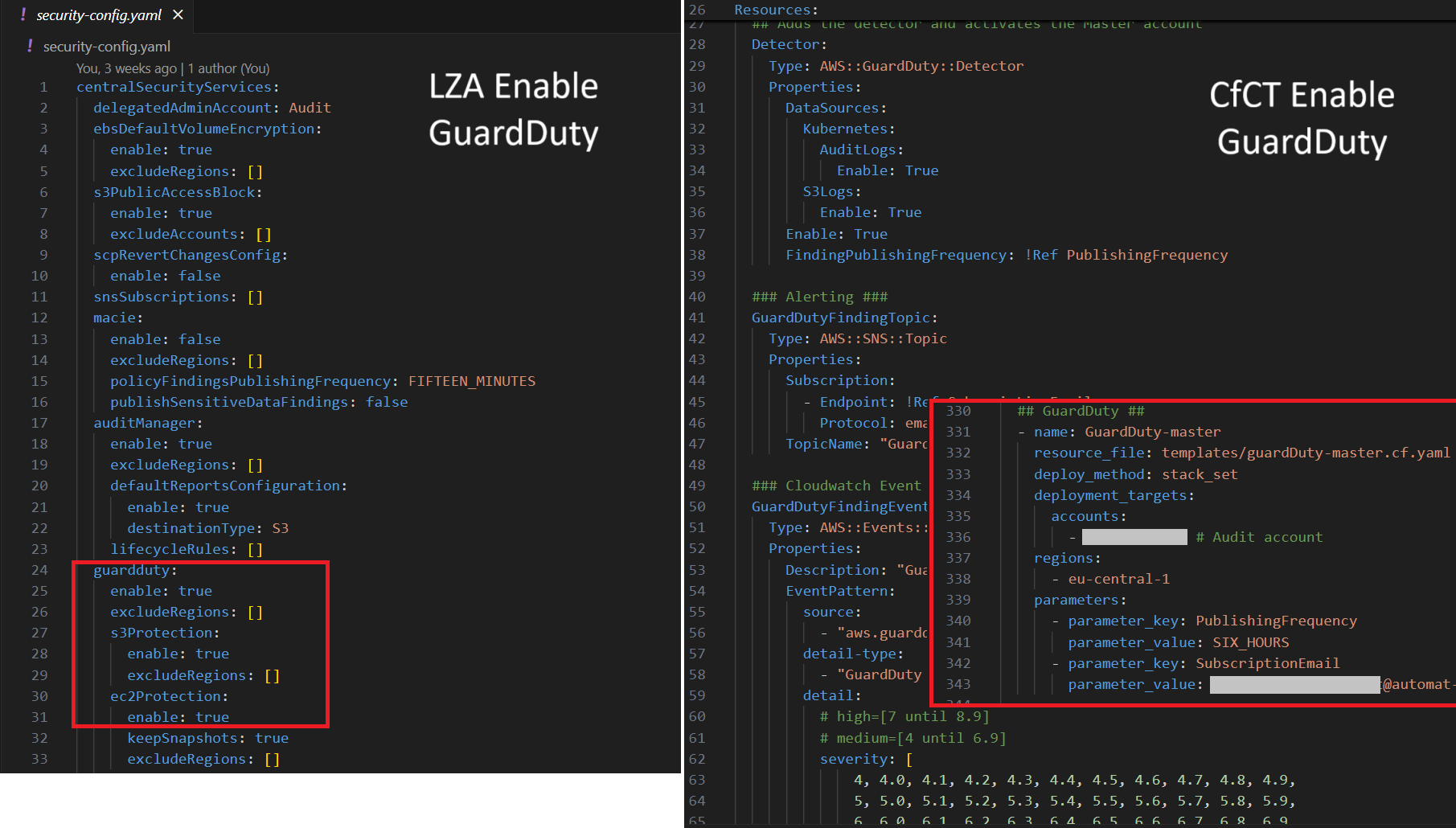
The same is with Macie, Audit Manager, Security Hub ^
Conclusion
Landing Zone Accelerator on AWS is a more advanced solution for customizing Landing Zones compared to Customizations for AWS Control Tower (CfCT). CfCT is more straightforward to understand because LZA has a lot of magic built into it, leveraging CDK and numerous Lambda Functions. However, due to this simplicity, CfCT has many limitations, whereas LZA enables the deployment of many essential features with just a couple of lines of code.
In the following posts, we will examine other LZA capabilities in detail.


